I had meant to write about this a couple days ago but just have been pretty busy. At Toorcon 12 I mentioned that the last talk I saw was about session hijacking (sidejacking) and they (Eric Butler and Ian Gallagher) released a pretty nifty tool that makes it really easy to steal a users session while on the same wifi AP. I downloaded it when I was at the airport and was the 14th person to download it. After checking this morning it has 373,535 downloads. That’s amazing and kind of frightening since I know what this tool can do.
So the theory isn’t that new, it’s been a problem for quite a while. I actually remember talking about this at a coffee shop with a friend while still in college. When accessing most popular sites that require logins you receive a HTTP session cookie from the server once you authenticate. The vulnerability is not about getting a users password and user name, because most times those are done using SSL and you aren’t able to sniff that data. The vulnerability comes into play when you move from a https page to a http page. (ie login page to regular non-encrypted page) When you log into a page and successfully authenticate, you are issued (or start) a session id(cookie) by the server. That id is used by the site to recognize you as the user you logged in as. It displays certain preferences and adds functionality when you are logged in to that site. If you can somehow steal that id(cookie) lets say over wifi or something, since everything is broadcast to everyone on that access point, you would then become that person to the website. So for example, if I was sniffing wireless traffic and was able to obtain someone’s facebook session and used that session id to go back to facebook, I would then see their account and would be logged in as that user.
So if that’s not a new vulnerability then why has it been so popular in the last few days?
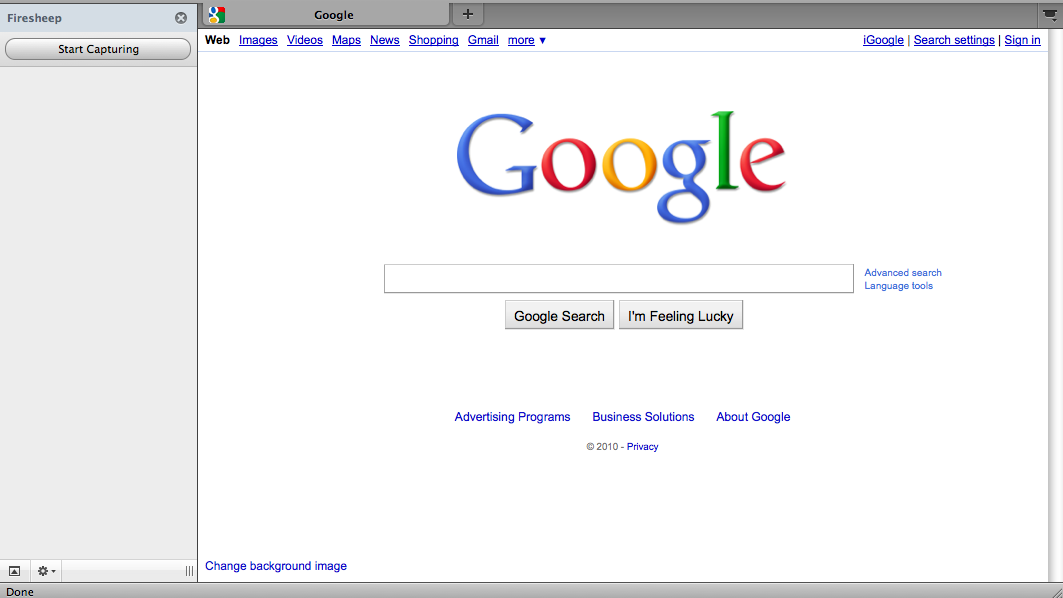
Firesheep. It’s a program that makes it super easy to do what I just described above automatically. No programming, or learning how to use packet tools, or loading cookies into your browser. I literally installed this firefox extension in less than 5 minutes. (Including DL time) The hardest part was trying to find out how to display the side bar.
So, like, how do I use this tool?
First, lets start with downloading the firefox extension. I’m using OS X but I’m pretty sure you can use Windows too but you have to install winpcap. You can download it here. Once you have it you can either open it with firefox or click on it and choose firefox as the application. Note: I had an older version of FF and I had to update my version before being able to install the extension. Once it’s installed, you can choose Tools -> Add-ons then find the Extensions tab. You should now see Firesheep 0.1 installed. Click preferences and check the Capture option to make sure that it’s pointed to your wireless device. (en0 for me) Websites is where you add new websites to the list of sites that you know how the session cookie is stored. Advanced is what type of traffic you would like to filer, default is TCP traffic on port 80. Once everything is setup you can then enable it by going to View -> Sidebar and then choosing Firesheep. You will then get a sidebar on the left hand side with a button that says start capturing. Once you start capturing people’s data and hijacking their sessions you are probably breaking one law or another depending on where you are. What you do at this point is up to you.
Can I protect against this?
Kinda. You can do a few things like VPN, tunnel http over ssh to a location that you know is legit, use ssl on the site if they have/allow it, or don’t access any of those sites while on public wifi. Those will definitely work but are not really convenient. I think the point of this tool was to make it so widespread for anyone to run this type of attack that it would force sites to use ssl for everything. So go complain to vulnerable sites that they need to improve their security.